This is the multi-page printable view of this section. Click here to print.
On-premise
- 1: Deployment guide
- 2: Authentication
- 3: Authorization
- 4: Prepare AxoRouter hosts
- 5: Upgrade
1 - Deployment guide
This guide shows you how to install AxoConsole on a local, on-premises virtual machine using k3s and Helm. Installation of other components like the NGINX ingress controller NS cert-manager is also included. Since this is a single instance deployment, we don’t recommend using it in production environments. For additional steps and configurations needed in production environments, contact our support team.
At a high level, the deployment consists of the following steps:
- Preparing a virtual machine.
- Installing Kubernetes on the virtual machine.
- Basic authentication with admin user and password is configured by default. This guide also shows you how to configure other common authentication methods like LDAP, Github and Google.
- Before deploying AxoRouter describes the steps you have to complete on a host before deploying AxoRouter on it. These steps are specific to on-premises AxoConsole deployments, and are not needed when using the SaaS AxoConsole.
Prerequisites
To install AxoConsole, you’ll need the following:
-
The URL for the AxoConsole Helm chart. You’ll receive this URL from our team. You can request it using the contact form.
CAUTION:
Don’t start the Install AxoConsole process until you’ve received the chart URL. -
A license key for AxoConsole. You’ll receive this from our team. You can request it using the contact form.
-
A host that meets the system requirements.
-
Network access set up for the host.
System requirements
Supported operating system: Ubuntu 24.04, Red Hat 9 and compatible (tested with AlmaLinux 9)
The virtual machine (VM) must have at least:
- 4 vCPUs (x86_64-based)
- 8 GB RAM
- 100 GB disk space
This setup can handle about 100 AxoRouter instances and 1000 data source hosts.
For reference, a real-life scenario that handles 100 AxoRouter and 3000 data source hosts with 30-day metric retention would need:
- 16 vCPU (x86_64-based)
- 16 GB RAM
- 250 GB disk space
For details on sizing, contact our support team.
You’ll need to have access to a user with sudo privileges.
Network access
The hosts must be able to access the following domains related to the AxoConsole:
-
When using AxoConsole SaaS:
<your-tenant-id>.cloud.axoflow.io: HTTPS traffic on TCP port 443, needed to download the binaries for Axoflow software (like Axolet and AxoRouter).kcp.<your-tenant-id>.cloud.axoflow.io: HTTPS (mutual TLS) traffic on TCP port 443 for management traffic.telemetry.<your-tenant-id>.cloud.axoflow.io: HTTPS (mutual TLS) traffic on TCP port 443, where Axolet sends the metrics of the host.us-docker.pkg.dev: HTTPS traffic on TCP port 443, for pulling container images (AxoRouter only).
-
When using an on-premise AxoConsole:
-
The following domains should point to AxoConsole IP address to access Axoflow from your desktop and AxoRouter hosts:
your-host.your-domain: The main domain of your AxoConsole deployment.authenticate.your-host.your-domain: A subdomain used for authentication.idp.your-host.your-domain: A subdomain for the identity provider.
-
The AxoConsole host must have the following Open Ports:
- Port 80 (HTTP)
- Port 443 (HTTPS)
-
-
When installing Axoflow agent for Windows or Linux:
github.com: HTTPS traffic on TCP port 443, for downloading installer packages.
Set up Kubernetes
Complete the following steps to install k3s and some dependencies on the virtual machine.
-
Run
getenforceto check the status of SELinux. -
Check the
/etc/selinux/configfile and make sure that the settings match the results of thegetenforceoutput (for example,SELINUX=disabled). K3S supports SELinux, but the installation can fail if there is a mismatch between the configured and actual settings. -
Install k3s.
-
Run the following command:
curl -sfL https://get.k3s.io | INSTALL_K3S_EXEC="--disable traefik --disable metrics-server" K3S_KUBECONFIG_MODE="644" sh -s - -
Check that the k3s service is running:
systemctl status k3s
-
-
Install the NGINX ingress controller.
NGINX_VERSION="v4.11.3" sudo tee /var/lib/rancher/k3s/server/manifests/ingress-nginx.yaml > /dev/null <<EOF --- apiVersion: helm.cattle.io/v1 kind: HelmChart metadata: name: ingress-nginx namespace: kube-system spec: createNamespace: true chart: ingress-nginx repo: https://kubernetes.github.io/ingress-nginx version: $NGINX_VERSION targetNamespace: ingress-nginx valuesContent: |- controller: extraArgs: enable-ssl-passthrough: true hostNetwork: true hostPort: enabled: true service: enabled: false admissionWebhooks: enabled: false updateStrategy: strategy: type: Recreate EOF -
Install the cert-manager controller.
-
Run the command:
CM_VERSION="1.16.2" sudo tee /var/lib/rancher/k3s/server/manifests/cert-manager.yaml > /dev/null <<EOF --- apiVersion: helm.cattle.io/v1 kind: HelmChart metadata: name: cert-manager namespace: kube-system spec: createNamespace: true chart: cert-manager version: $CM_VERSION repo: https://charts.jetstack.io targetNamespace: cert-manager valuesContent: |- crds: enabled: true enableCertificateOwnerRef: true EOF -
Wait for the helm chart to be installed:
while ! kubectl get job helm-install-cert-manager -n kube-system; do sleep 1 done kubectl wait --for=condition=complete job/helm-install-cert-manager -n kube-system --timeout=300s
-
Install the AxoConsole
Complete the following steps to deploy the AxoConsole Helm chart.
-
Set the following environment variables as needed for your deployment.
-
The domain name for your AxoConsole deployment. This must point to the IP address of the VM you’re installing AxoConsole on.
BASE_HOSTNAME=your-host.your-domainNote To use Google authentication, AxoConsole must be deployed on a publicly accessible domain name (the$BASE_HOSTNAMEmust end with a valid top-level domain, for example,.comor.io.) -
The license key of AxoConsole. You’ll receive this from our team. You can request it using the contact form.
LICENSE_KEY="your-license-key" -
The version number of AxoConsole you want to deploy.
VERSION="0.78.0" -
The internal IP address of the virtual machine. This is needed so the authentication service can communicate with the identity provider without relying on DNS.
VM_IP_ADDRESS=$(hostname -I | cut -d' ' -f1)Check that the above command returned the correct IP, it might not be accurate if the host has multiple IP addresses.
-
The URL of the Axoflow Helm chart. You’ll receive this URL from our team. You can request it using the contact form.
AXOFLOW_HELM_CHART_URL="<the-chart-URL-received-from-Axoflow>"
-
-
Install AxoConsole. You can either let the chart create a password, or you can set an email and password manually.
-
Add password automatically: The following configuration file enables automatic password creation. If this basic setup is working, you can configure another authentication provider.
sudo tee /var/lib/rancher/k3s/server/manifests/axoflow.yaml > /dev/null <<EOF --- apiVersion: helm.cattle.io/v1 kind: HelmChart metadata: name: axoflow namespace: kube-system spec: createNamespace: true targetNamespace: axoflow version: $VERSION chart: $AXOFLOW_HELM_CHART_URL failurePolicy: abort valuesContent: |- baseHostName: $BASE_HOSTNAME licenseKey: $LICENSE_KEY dex: localIP: $VM_IP_ADDRESS EOFTo reclaim your autogenerated password, use the following command.
kubectl -n axoflow get secret axoflow-admin -o go-template='Email: {{ .data.email | base64decode }}{{ printf "\n" }}Password: {{ .data.password | base64decode }}{{ printf "\n" }}'Record the email and password, you’ll need it to log in to AxoConsole.
-
Set password manually: If you’d like to set the email/password manually, create the secret storing the required information, then set a unique identifier for the administrator user using
uuidgen. Note that:- On Ubuntu, you must first install the
uuid-runtimepackage by runningsudo apt install uuid-runtime. - To set the bcrypt hash of the administrator password, you can generate it with the
htpasswdtool, which is part of thehttpd-toolspackage on Red Hat (install it usingsudo dnf install httpd-tools), and theapache2-utilspackage on Ubuntu (install it usingsudo apt install apache2-utils).
ADMIN_USERNAME="<your admin username>" ADMIN_EMAIL="<your admin email>" ADMIN_PASSWORD="<your admin password>" ADMIN_UUID=$(uuidgen) ADMIN_PASSWORD_HASH=$(echo $ADMIN_PASSWORD | htpasswd -BinC 10 $ADMIN_USERNAME | cut -d: -f2) sudo tee /var/lib/rancher/k3s/server/manifests/axoflow.yaml > /dev/null <<EOF --- apiVersion: helm.cattle.io/v1 kind: HelmChart metadata: name: axoflow namespace: kube-system spec: createNamespace: true targetNamespace: axoflow version: $VERSION chart: $AXOFLOW_HELM_CHART_URL failurePolicy: abort valuesContent: |- baseHostName: $BASE_HOSTNAME licenseKey: $LICENSE_KEY pomerium: policy: emails: - $ADMIN_EMAIL dex: localIP: $VM_IP_ADDRESS defaultCredential: create: false EOF kubectl -n axoflow create secret generic axoflow-admin --from-literal=username=$ADMIN_USERNAME --from-literal=password_hash=$ADMIN_PASSWORD_HASH --from-literal=email=$ADMIN_EMAIL --from-literal=uuid=$ADMIN_UUID - On Ubuntu, you must first install the
-
-
Wait a few minutes until everything is installed. Check that every component has been installed and is running:
kubectl get pods -AThe output should be similar to:
NAMESPACE NAME READY STATUS RESTARTS AGE axoflow axolet-dist-55ccbc4759-q7l7n 1/1 Running 0 2d3h axoflow chalco-6cfc74b4fb-mwbbz 1/1 Running 0 2d3h axoflow configure-kcp-1-x6js6 0/1 Completed 2 2d3h axoflow configure-kcp-cert-manager-1-wvhhp 0/1 Completed 1 2d3h axoflow configure-kcp-token-1-xggg7 0/1 Completed 1 2d3h axoflow controller-manager-5ff8d5ffd-f6xtq 1/1 Running 0 2d3h axoflow dex-5b9d7b88b-bv82d 1/1 Running 0 2d3h axoflow kcp-0 1/1 Running 1 (2d3h ago) 2d3h axoflow kcp-cert-manager-0 1/1 Running 0 2d3h axoflow pomerium-56b8b9b6b9-vt4t8 1/1 Running 0 2d3h axoflow prometheus-server-0 2/2 Running 0 2d3h axoflow telemetryproxy-65f77dcf66-4xr6b 1/1 Running 0 2d3h axoflow ui-6dc7bdb4c5-frn2p 2/2 Running 0 2d3h cert-manager cert-manager-74c755695c-5fs6v 1/1 Running 5 (144m ago) 2d3h cert-manager cert-manager-cainjector-dcc5966bc-9kn4s 1/1 Running 0 2d3h cert-manager cert-manager-webhook-dfb76c7bd-z9kqr 1/1 Running 0 2d3h ingress-nginx ingress-nginx-controller-bcc7fb5bd-n5htp 1/1 Running 0 2d3h kube-system coredns-ccb96694c-fhk8f 1/1 Running 0 2d3h kube-system helm-install-axoflow-b9crk 0/1 Completed 0 2d3h kube-system helm-install-cert-manager-88lt7 0/1 Completed 0 2d3h kube-system helm-install-ingress-nginx-qvkhf 0/1 Completed 0 2d3h kube-system local-path-provisioner-5cf85fd84d-xdlnr 1/1 Running 0 2d3h(For details on what the different services do, see the service reference.)
Login to AxoConsole
-
If the domain name of AxoConsole cannot be resolved from your desktop, add it to the
/etc/hostsfile in the following format. Use and IP address of AxoConsole that can be accessed from your desktop.<AXOFLOW-CONSOLE-IP-ADDRESS> <your-host.your-domain> idp.<your-host.your-domain> authenticate.<your-host.your-domain> -
Open the
https://<your-host.your-domain>URL in your browser. -
The on-premise deployment of AxoConsole shows a self-signed certificate. If your browser complains about the related risks, accept it.
-
Use the email address and password you got or set in the installation step to log in to AxoConsole.
Prepare AxoRouter hosts
AxoConsole service reference
| Service Name | Namespace | Purposes | Function |
|---|---|---|---|
| KCP | axoflow |
Backend API | Kubernetes Like Service with built in database, that service manage all the settings that our system manage |
| Chalco | axoflow |
Frontend API | Serve the UI API Calls, implement business logic for the UI |
| Controller-Manager | axoflow |
Backend Service | Reacts to state changes in our business entities, manage business logic for the Backend |
| Telemetry Proxy | axoflow |
Backend API | Receives agents telemetries |
| UI | axoflow |
Dashboard | The frontend for AxoConsole |
| Prometheus | axoflow |
Backend API /Service | Monitoring component to store time series information and an API for query, manage alert rules |
| Alertmanager | axoflow |
Backend API /Service | Monitoring component to Send alert based on alerting rules |
| Dex | axoflow |
Identity Connector/Proxy | Identity Connector/Proxy to allow the customer to use own identity (Google, Ldap, etc.) |
| Pomerium | axoflow |
HTTP Proxy | Allow policy based access to the Frontend API (Chalco) |
| Axolet Dist | axoflow |
Backend API | Static artifact store to contains agents binaries |
| Cert Manager (kcp) | axoflow |
Automated Certificate management tool | Manage certificates for Agents |
| Cert Manager | cert-manager |
Automated Certificate management tool | Manage certificates for Axoflow components (Backend API, HTTP Proxy) |
| NGINX Ingress Controller | ingress-nginx |
HTTP Proxy | Allow routing the HTTP traffic between multiple Frontend/Backend API |
2 - Authentication
These sections show you how to configure on-premises and Kubernetes deployments of AxoConsole to use different authentication backends.
2.1 - GitHub
This section shows you how to use GitHub OAuth2 as an authentication backend for AxoConsole. It is assumed that you already have a GitHub organization. Complete the following steps.
Prerequisites
Register a new OAuth GitHub application for your organization. (For testing, you can create it under your personal account.) Make sure to:
-
Set the Homepage URL to the URL of your AxoConsole deployment:
https://<your-console-host.your-domain>/callback, for example,https://axoflow-console.example.com. -
Set the Authorization callback URL to:
https://auth.<your-console-host.your-domain>/callback, for example,https://auth.axoflow-console.example.com/callback.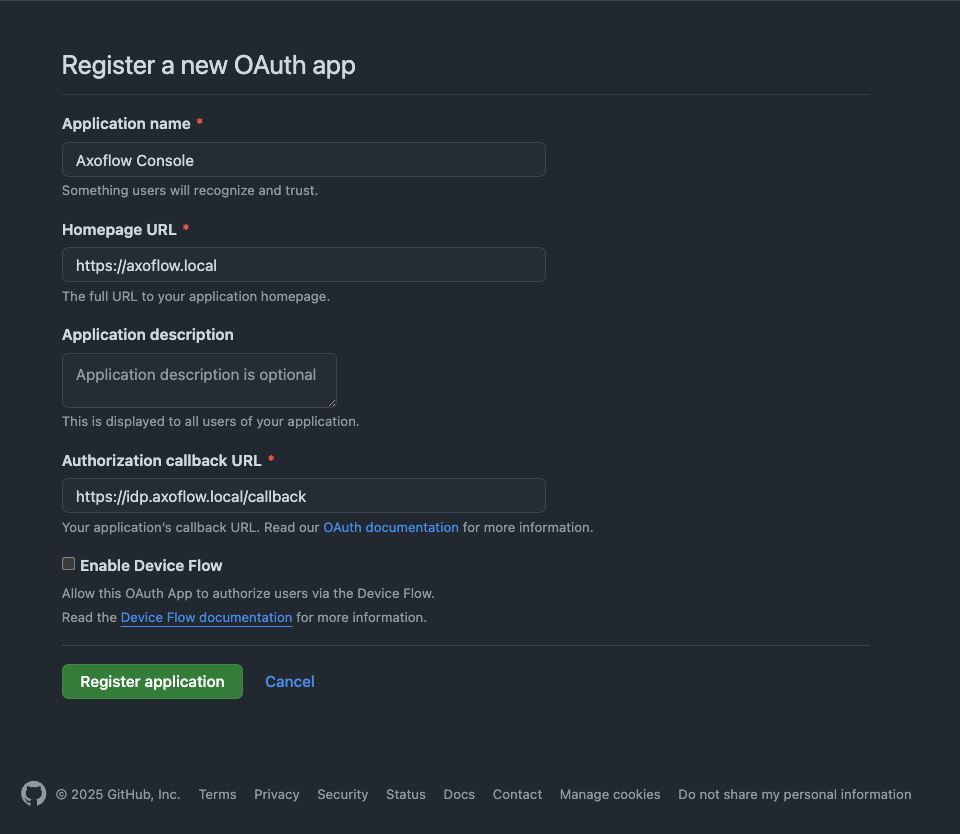
-
Save the Client id of the app, you’ll need it to configure AxoConsole.
-
Generate a Client secret and save it, you’ll need it to configure AxoConsole.
Configuration
-
Verify that Dex is configured as the OIDC provider in the
/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile:chalco.oidc.enabled: truechalco.oidc.provider: "dex"
For example:
oidc: enabled: true provider: "dex" -
Configure authentication by editing the
spec.dex.configsection of the/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile.-
(Optional) If you’ve used our earlier example, delete the
spec.dex.config.staticPasswordssection. -
Add the
spec.dex.config.connectorssection to the file, like this:dex: enabled: true localIP: $VM_IP_ADDRESS config: create: true connectors: - type: github # Required field for connector id. id: github # Required field for connector name. name: GitHub config: # Credentials can be string literals or pulled from the environment. clientID: <ID-of-GitHub-application> clientSecret: <Secret-of-GitHub-application> redirectURI: <idp.your-host.your-domain/callback> orgs: - name: <your-GitHub-organization>Note that if you have a valid domain name that points to the VM, you can omit the
localIP: $VM_IP_ADDRESSline. -
Edit the following fields. For details on the configuration parameters, see the Dex GitHub connector documentation.
connectors.config.clientID: The ID of the GitHub OAuth application.connectors.config.clientSecret: The client secret of the GitHub OAuth application.connectors.config.redirectURI: The callback URL of the GitHub OAuth application:https://auth.<your-console-host.your-domain>/callback, for example,https://auth.axoflow-console.example.com/callback.- If you want to fetch every GitHub group, replace the entire
orgssection with theloadAllGroups: true connectors.config.orgs: List of the GitHub organizations whose members can access AxoConsole. Restrict access to your organization.
-
-
Configure authorization in the
kcp.rbac.rolessection of the/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile.The following roles are available in AxoConsole by default:
-
IAMadmin: Can manage the roles and permissions to access AxoConsole. Only this role can make changes on the Settings > Roles page. -
admin: Has full access to AxoConsole, but has only read access to the Settings > Roles page. -
infrastructureManager: Can manage the infrastructure (without the permissions to view or tap log contents, or to rehydrate data). Has full access to the following pages: Activity Logs, Alerting, Routers, Sources, Flows, Provisioning, Search Logs. Can tap into service logs. -
infrastructureViewer: Similar to infrastructure-manager, but can only view the pages. Can tap into service logs. -
contentManager: Can view log content and manage content related details like flows (without the permissions to manage infrastructure, but including access to view infrastructure details).- Has full access to the Rehydration page.
- Can view and modify Flows, but can’t create or delete them.
- Can view Routers, Sources, Search Logs, Analytics.
- Can tap into logs.
-
contentViewer: Can view content like analytics, log search, log tapping (without the permissions to manage or view infrastructure details).- Can view Search Logs, Analytics.
- Can tap into logs.
If you need other roles, contact the Axoflow support team. Composing other roles is possible as part of a custom integration.
You can use email addresses or GitHub groups to assign your users to AxoConsole user roles.
To use the groups fetched from GitHub, prefix the name of the GitHub group with
groups:, and add them to the related roles underkcp.rbac.roles.<role>.groups. For example:rbac: createRoles: true createRoleBindings: true roles: IAMadmin: groups: - groups:iamadmin admin: groups: - groups:admins contentViewer: groups: - groups:readonly-
A specific email address, for example,
email:username@example.comNote- The user must be able to authenticate to AxoConsole using this email address, so authentication must be properly set up.
- Multiple identity providers may allow authentication with the same email address, possibly with different level of ownership validation.
-
An entire email domain, for example,
emaildomain:example.com. Any user who authenticates with an email address belonging to this email domain will have access to the role. -
A user group. The format of the group depends on the OID provider.
- If you’re using AxoConsole as a SaaS, specify the group in the following format:
cognito:groups:<groupname-retrieved-from-cognito>, for example,cognito:groups:ExampleGoogleSaml:Operator. - If you’re using an on-prem AxoConsole deployment, specify the group in the following format:
groups:<groupname-retrieved-from-dex>for example,groups:operator.
- If you’re using AxoConsole as a SaaS, specify the group in the following format:
-
A specific session of an authenticated user, in the following format:
user:<oidc-response-subject>, for example:user:42c4e962-f077-705f-138f-f01ba1220c44. -
Every authenticated user:
axoflow:user
For details on authorization settings, see Authorization.
-
-
Save the file.
-
Restart the dex deployment after changing the connector:
kubectl rollout restart deployment/dex -n axoflowExpected output:
deployment.apps/dex restarted -
Open the main page of your AxoConsole deployment in your browser. You’ll be redirected to the GitHub authentication page.
After completing the GitHub authentication you can access AxoConsole.
Getting help
You can troubleshoot common errors by running kubectl logs -n axoflow <dex-container-name>
If you run into problems setting up the authentication or authorization, contact our support team.
2.2 - Google
This section shows you how to use Google OpenID Connect as an authentication backend for AxoConsole. It is assumed that you already have a Google organization and Google Cloud Console access. Complete the following steps.
Prerequisites
-
To use Google authentication, AxoConsole must be deployed on a publicly accessible domain name (the
$BASE_HOSTNAMEmust end with a valid top-level domain, for example,.comor.io.) -
Configure OpenID Connect and create an OpenID credential for a Web application.
- Make sure to set the Authorized redirect URIs to:
https://auth.<your-console-host.your-domain>/callback, for example,https://auth.axoflow-console.example.com/callback. - Save the Client ID of the app and the Client secret of the application, you’ll need them to configure AxoConsole.
For details on setting up OpenID Connect, see the official documentation.
- Make sure to set the Authorized redirect URIs to:
Google group membership
To use group memberships when assigning your users to AxoConsole user roles, you have to configure a service account to retrieve group memberships. Otherwise, you can use email domains. To set up a proper service account, complete the following steps.
- Set up a service account with Domain-Wide Delegation.
- Save the JSON key file that contains the authentication information for the service account. You’ll need it later.
- Delegate the
https://www.googleapis.com/auth/admin.directory.group.readonlyscope to the service account. Do not delegate any other scope. - Enable the Admin SDK.
You’ll also need the email address of a Google Workspace user with a minimum of the Groups Reader Role assigned. The service account will impersonate this user when making calls to the admin API.
Configuration
-
Verify that Dex is configured as the OIDC provider in the
/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile:chalco.oidc.enabled: truechalco.oidc.provider: "dex"
For example:
oidc: enabled: true provider: "dex" -
Configure authentication by editing the
spec.dex.configsection of the/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile.-
(Optional) If you’ve used our earlier example, delete the
spec.dex.config.staticPasswordssection. -
Add the
spec.dex.config.connectorssection to the file, like this:connectors: - type: google id: google name: Google config: # Connector config values starting with a "$" will read from the environment. clientID: <ID-of-Google-application> clientSecret: <Secret-of-GitHub-application> # Dex's issuer URL + "/callback" redirectURI: <idp.your-host.your-domain/callback> # Set the value of `prompt` query parameter in the authorization request # The default value is "consent" when not set. promptType: consent # Google supports whitelisting allowed domains when using G Suite # (Google Apps). The following field can be set to a list of domains # that can log in: # hostedDomains: - <your-domain> # For group membership authorization: #serviceAccountFilePath: "/etc/dex/sa-file/service-account.json" #domainToAdminEmail: #"*": <impersonated-group-reader-email-address> -
Edit the following fields. For details on the configuration parameters, see the Dex Google connector documentation.
connectors.config.clientID: The ID of the Google application.connectors.config.clientSecret: The client secret of the Google application.connectors.config.redirectURI: The callback URL of the Google application:https://auth.<your-console-host.your-domain>/callback, for example,https://auth.axoflow-console.example.com/callback.connectors.config.hostedDomains: The domain where AxoConsole is deployed, for example,example.com. Your users must have email addresses for this domain at Google.
-
If you’ll use Google group memberships for authorization, uncomment the
serviceAccountFilePathanddomainToAdminEmailsections. Replace<impersonated-group-reader-email-address>with the email address you created in Google group memberships prerequisites.# For group membership authorization: serviceAccountFilePath: "/etc/dex/sa-file/service-account.json" domainToAdminEmail: "*": <impersonated-group-reader-email-address>
-
-
Configure authorization in the
kcp.rbac.rolessection of the/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile.The following roles are available in AxoConsole by default:
-
IAMadmin: Can manage the roles and permissions to access AxoConsole. Only this role can make changes on the Settings > Roles page. -
admin: Has full access to AxoConsole, but has only read access to the Settings > Roles page. -
infrastructureManager: Can manage the infrastructure (without the permissions to view or tap log contents, or to rehydrate data). Has full access to the following pages: Activity Logs, Alerting, Routers, Sources, Flows, Provisioning, Search Logs. Can tap into service logs. -
infrastructureViewer: Similar to infrastructure-manager, but can only view the pages. Can tap into service logs. -
contentManager: Can view log content and manage content related details like flows (without the permissions to manage infrastructure, but including access to view infrastructure details).- Has full access to the Rehydration page.
- Can view and modify Flows, but can’t create or delete them.
- Can view Routers, Sources, Search Logs, Analytics.
- Can tap into logs.
-
contentViewer: Can view content like analytics, log search, log tapping (without the permissions to manage or view infrastructure details).- Can view Search Logs, Analytics.
- Can tap into logs.
If you need other roles, contact the Axoflow support team. Composing other roles is possible as part of a custom integration.
To assign Google groups to AxoConsole roles, add the groups of your users to the related roles under
kcp.rbac.roles.<role>.groups.Note Make sure that you’ve completed the prerequisites detailed in Google group membership.rbac: createRoles: true createRoleBindings: true roles: IAMadmin: groups: - groups:iamadmin@example.com admin: groups: - groups:admin@example.com contentViewer: groups: - groups:readonly@example.com-
A specific email address, for example,
email:username@example.comNote- The user must be able to authenticate to AxoConsole using this email address, so authentication must be properly set up.
- Multiple identity providers may allow authentication with the same email address, possibly with different level of ownership validation.
-
An entire email domain, for example,
emaildomain:example.com. Any user who authenticates with an email address belonging to this email domain will have access to the role. -
A user group. The format of the group depends on the OID provider.
- If you’re using AxoConsole as a SaaS, specify the group in the following format:
cognito:groups:<groupname-retrieved-from-cognito>, for example,cognito:groups:ExampleGoogleSaml:Operator. - If you’re using an on-prem AxoConsole deployment, specify the group in the following format:
groups:<groupname-retrieved-from-dex>for example,groups:operator.
- If you’re using AxoConsole as a SaaS, specify the group in the following format:
-
A specific session of an authenticated user, in the following format:
user:<oidc-response-subject>, for example:user:42c4e962-f077-705f-138f-f01ba1220c44. -
Every authenticated user:
axoflow:user
For details on authorization settings, see Authorization.
-
-
Save the file.
-
If you’re using Google groups to assign user roles, complete the following steps.
-
Run the following command to delete the
dex-google-service-accountsecret. This is a placeholder secret that you’ll re-create with valid values in the next step.kubectl -n axoflow delete secret dex-google-service-account -
Re-create the secret using the JSON key of the Google service account you’ve created in Google group membership.
kubectl -n axoflow create secret dex-google-service-account --from-file <path-to-the-JSON-key>Expected output:
secret/dex-google-service-account created -
Edit the
/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile and set thedex.googleServiceAccount.createoption tofalse.
-
-
Restart the dex deployment after changing the connector:
kubectl rollout restart deployment/dex -n axoflowExpected output:
deployment.apps/dex restarted -
Open the main page of your AxoConsole deployment in your browser. You’ll be redirected to the Google authentication page.
After completing the Google authentication you can access AxoConsole.
Getting help
You can troubleshoot common errors by running kubectl logs -n axoflow <dex-container-name>
If you run into problems setting up the authentication or authorization, contact our support team.
2.3 - LDAP
This section shows you how to use LDAP as an authentication backend for AxoConsole. In the examples we used the public demo service of FreeIPA as an LDAP server. It is assumed that you already have an LDAP server in place. Complete the following steps.
-
Verify that Dex is configured as the OIDC provider in the
/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile:chalco.oidc.enabled: truechalco.oidc.provider: "dex"
For example:
oidc: enabled: true provider: "dex" -
Configure authentication by editing the
spec.dex.configsection of the/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile.-
(Optional) If you’ve used our earlier example, delete the
spec.dex.config.staticPasswordssection. -
Add the
spec.dex.config.connectorssection to the file, like this:CAUTION:
This example shows a simple configuration suitable for testing. In production environments, make sure to:
- configure TLS encryption to access your LDAP server
- retrieve the bind password from a vault or environment variable. Note that if the bind password contains the
$character, you must set it in an environment variable and pass it likebindPW: $LDAP_BINDPW.
dex: enabled: true localIP: $VM_IP_ADDRESS config: create: true connectors: - type: ldap name: OpenLDAP id: ldap config: host: ipa.demo1.freeipa.org insecureNoSSL: true # This would normally be a read-only user. bindDN: uid=admin,cn=users,cn=accounts,dc=demo1,dc=freeipa,dc=org bindPW: Secret123 usernamePrompt: Email Address userSearch: baseDN: dc=demo1,dc=freeipa,dc=org filter: "(objectClass=person)" username: mail # "DN" (case sensitive) is a special attribute name. It indicates that # this value should be taken from the entity's DN not an attribute on # the entity. idAttr: uid emailAttr: mail nameAttr: cn groupSearch: baseDN: dc=demo1,dc=freeipa,dc=org filter: "(objectClass=groupOfNames)" userMatchers: # A user is a member of a group when their DN matches # the value of a "member" attribute on the group entity. - userAttr: DN groupAttr: member # The group name should be the "cn" value. nameAttr: cn -
Edit the following fields. For details on the configuration parameters, see the Dex LDAP connector documentation.
connectors.config.host: The hostname and optionally the port of the LDAP server in “host:port” format.connectors.config.bindDNandconnectors.config.bindPW: The DN and password for an application service account that the connector uses to search for users and groups.connectors.config.userSearch.bindDNandconnectors.config.groupSearch.bindDN: The base DN for the user and group search.
-
-
Configure authorization in the
kcp.rbac.rolessection of the/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile.The following roles are available in AxoConsole by default:
-
IAMadmin: Can manage the roles and permissions to access AxoConsole. Only this role can make changes on the Settings > Roles page. -
admin: Has full access to AxoConsole, but has only read access to the Settings > Roles page. -
infrastructureManager: Can manage the infrastructure (without the permissions to view or tap log contents, or to rehydrate data). Has full access to the following pages: Activity Logs, Alerting, Routers, Sources, Flows, Provisioning, Search Logs. Can tap into service logs. -
infrastructureViewer: Similar to infrastructure-manager, but can only view the pages. Can tap into service logs. -
contentManager: Can view log content and manage content related details like flows (without the permissions to manage infrastructure, but including access to view infrastructure details).- Has full access to the Rehydration page.
- Can view and modify Flows, but can’t create or delete them.
- Can view Routers, Sources, Search Logs, Analytics.
- Can tap into logs.
-
contentViewer: Can view content like analytics, log search, log tapping (without the permissions to manage or view infrastructure details).- Can view Search Logs, Analytics.
- Can tap into logs.
If you need other roles, contact the Axoflow support team. Composing other roles is possible as part of a custom integration.
- Add the names of the LDAP groups to the related roles under
kcp.rbac.roles.<role>.groups. In the following example, themanagersgroup gets administrator role, and thereadonlygroup gets read-only access to AxoConsole.
rbac: createRoles: true createRoleBindings: true roles: IAMadmin: groups: - groups:iamadmin admin: groups: - groups:managers contentViewer: groups: - groups:readonly-
A specific email address, for example,
email:username@example.comNote- The user must be able to authenticate to AxoConsole using this email address, so authentication must be properly set up.
- Multiple identity providers may allow authentication with the same email address, possibly with different level of ownership validation.
-
An entire email domain, for example,
emaildomain:example.com. Any user who authenticates with an email address belonging to this email domain will have access to the role. -
A user group. The format of the group depends on the OID provider.
- If you’re using AxoConsole as a SaaS, specify the group in the following format:
cognito:groups:<groupname-retrieved-from-cognito>, for example,cognito:groups:ExampleGoogleSaml:Operator. - If you’re using an on-prem AxoConsole deployment, specify the group in the following format:
groups:<groupname-retrieved-from-dex>for example,groups:operator.
- If you’re using AxoConsole as a SaaS, specify the group in the following format:
-
A specific session of an authenticated user, in the following format:
user:<oidc-response-subject>, for example:user:42c4e962-f077-705f-138f-f01ba1220c44. -
Every authenticated user:
axoflow:user
For details on authorization settings, see Authorization.
-
-
Save the file.
-
Restart the dex deployment after changing the connector:
kubectl rollout restart deployment/dex -n axoflowExpected output:
deployment.apps/dex restarted
Getting help
You can troubleshoot common errors by running kubectl logs -n axoflow <dex-container-name>
If you run into problems setting up the authentication or authorization, contact our support team.
3 - Authorization
These sections show you how to configure the authorization of AxoConsole with different authentication backends.
You can configure authorization in the spec.pomerium.policy section of the AxoConsole manifest. In on-premise deployments, the manifest is in the /var/lib/rancher/k3s/server/manifests/axoflow.yaml file.
You can list individual email addresses and user groups to have read and write (using the keys under spec.pomerium.policy) and read-only (using the keys under spec.pomerium.policy.readOnly) access to AxoConsole. Which key to use depends on the authentication backend configured for AxoConsole:
-
emails: Email addresses used with static passwords and GitHub authentication.With GitHub authentication, use the primary GitHub email addresses of your users, otherwise the authorization will fail.
-
claim/groups: LDAP groups used with LDAP authentication. For example:policy: emails: [] domains: [] groups: [] claim/groups: - managers readOnly: emails: [] domains: [] groups: [] claim/groups: - employee
4 - Prepare AxoRouter hosts
When using AxoRouter with an on-premises AxoConsole deployment, you have to complete the following steps on the hosts you want to deploy AxoRouter on. These steps are specific to on-premises AxoConsole deployments, and are not needed when using the SaaS AxoConsole.
-
If the domain name of AxoConsole cannot be resolved from the AxoRouter host, add it to the
/etc/hostsfile of the AxoRouter host in the following format. Use and IP address of AxoConsole that can be accessed from the AxoRouter host.<AXOFLOW-CONSOLE-IP-ADDRESS> <AXOFLOW-CONSOLE-BASE-URL> kcp.<AXOFLOW-CONSOLE-BASE-URL> telemetry.<AXOFLOW-CONSOLE-BASE-URL> idp.<AXOFLOW-CONSOLE-BASE-URL> authenticate.<AXOFLOW-CONSOLE-BASE-URL> -
Import AxoConsole certificates to AxoRouter hosts.
-
On the AxoConsole host: Run the following command to extract the AxoConsole CA certificate. The AxoRouter host will need this certificate to download the installation binaries.
kubectl get secret -n axoflow pomerium-certificates -o=jsonpath='{.data.ca\.crt}'|base64 -d > axoflow-ca.crtCopy this file to the AxoRouter hosts.
-
On the AxoRouter hosts: Copy the certificate file extracted from the AxoConsole host.
- On Red Hat: Copy the files into the
/etc/pki/ca-trust/source/anchors/folder, then runsudo update-ca-trust extract. (If needed, install theca-certificatespackage.) - On Ubuntu: Copy the files into the
/usr/local/share/ca-certificates/folder, then runsudo update-ca-certificates
- On Red Hat: Copy the files into the
-
-
curl -I https://<your-host.your-domain>should give you a valid HTTP/2 302 response -
Now you can deploy AxoRouter on the host.
5 - Upgrade
To upgrade an on-prem AxoConsole deployment, complete the following steps.
-
Log in to the host running AxoConsole.
-
Run the following command to update the version number in the
/var/lib/rancher/k3s/server/manifests/axoflow.yamlfile to 0.78.0.sudo sed -i.old -E 's/^( *version: ).*/\10.78.0/' /var/lib/rancher/k3s/server/manifests/axoflow.yaml -
Wait a few minutes until the pods are restarted. You can check their status by running:
kubectl get pods -A -
If everything is working as expected, re-deploy your AxoRouter and Axoflow agent instances to upgrade them.
In case you experience problems during the upgrade, contact our support team.