# SonicWall
SonicWall: Delivers firewall, VPN, and deep packet inspection to protect networks from cyber threats and intrusions.
The following sections show you how to configure [SonicWall firewalls]() to send their log data to Axoflow.
**CAUTION:**
Make sure to set data forwarding on your appliances/servers as described in this guide. Different settings like alternate message formats or ports might be valid, but can result in data loss or incorrect parsing.
## Prerequisites
* You have administrative access to the firewall.
* The date, time, and time zone are correctly set on the firewall.
* You have an [AxoRouter deployed and configured](../../../../docs/axoflow/provisioning/axorouter/index.md) with a [Syslog connector](../../../../docs/axoflow/data-sources/syslog/index.md) that has parsing and classification enabled (by default, every AxoRouter has such connectors). This device is going to receive the data from the firewall.
* You know the IP address the AxoRouter. To find it:
1. Open the AxoConsole.
2. Select the **Routers** or the **Topology** page.
3. Select on AxoRouter instance that is going to receive the logs.
4. Check the **Networks > Address** field.
## Steps for SonicOS 7.x
Note: The steps involving the SonicWall user interface are just for your convenience, for details, see the [official SonicWall documentation]().
1. Log in to your SonicWall device. You need administrator privileges to perform the configuration.
2. Register the address of your AxoRouter as an Address Object.
1. Select **MENU > OBJECT**.
2. Select **Match Objects > Addresses > Address objects**.
3. Click **Add Address**.
4. Configure the following settings:
* **Name** : Enter a name for the AxoRouter, for example, `AxoRouter`.
* **Zone Assignment** : Select the correct zone.
* **Type** : Select **Host**.
* **IP Address** : Enter the IP address of your AxoRouter: `%axorouter-ip%`
5. Click **Save**.
3. Set your AxoRouter as a syslog server.
1. Navigate to **Device > Log > Syslog**.
2. Select the **Syslog Servers** tab.
3. Click **Add**.
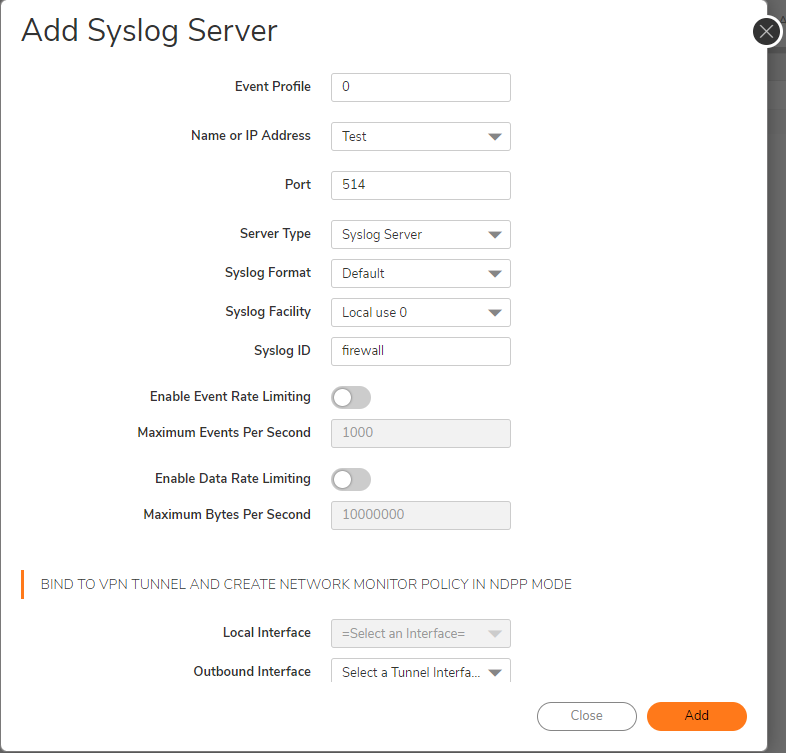
4. Configure the following options:
* **Name or IP Address** : Select the Address Object of AxoRouter.
* **Server Type** : Select **Syslog Server**.
* **Syslog Format** : Select **Enhanced**.
If your Syslog server does not use default port 514, type the port number in the **Port** field.
By default, AxoRouter accepts data on the following ports (unless you’ve modified the default connector rules):
* 514 UDP and TCP for RFC3164 (BSD-syslog) and RFC5424 (IETF-syslog) formatted traffic. AxoRouter automatically recognizes and handles both formats.
* 601 TCP for RFC5424 (IETF-syslog) and RFC3164 (BSD-syslog) formatted traffic. AxoRouter automatically recognizes and handles both formats.
* 6514 TCP for TLS-encrypted syslog traffic.
* 4317 TCP for OpenTelemetry log data.
To receive data on other ports or other protocols, configure other [connector rules](../../../../docs/axoflow/data-sources/connector-rules/index.md) for the AxoRouter host.
For TLS-encrypted syslog connections, create a new [connector rule](../../../../docs/axoflow/data-sources/connector-rules/index.md) or edit an existing one, and configure the keys and certificates needed to encrypt the connections. For details, see [Syslog](../../../../docs/axoflow/data-sources/syslog/index.md).
Note Make sure to enable the ports you’re using on the firewall of your host.
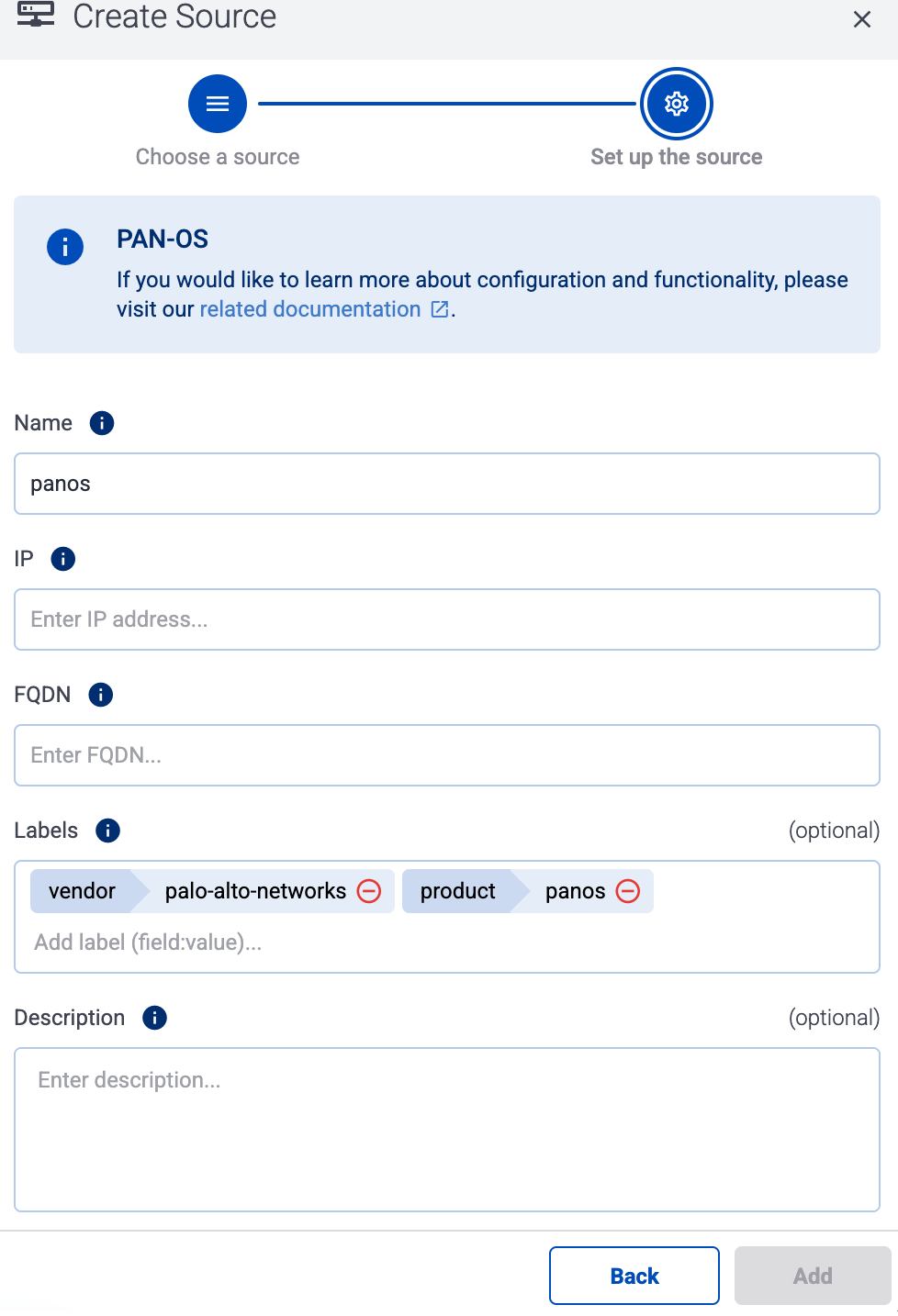
4. Add the source to AxoConsole.
1. Open the AxoConsole and select **Topology**.
2. Select **Add Item > Source**.
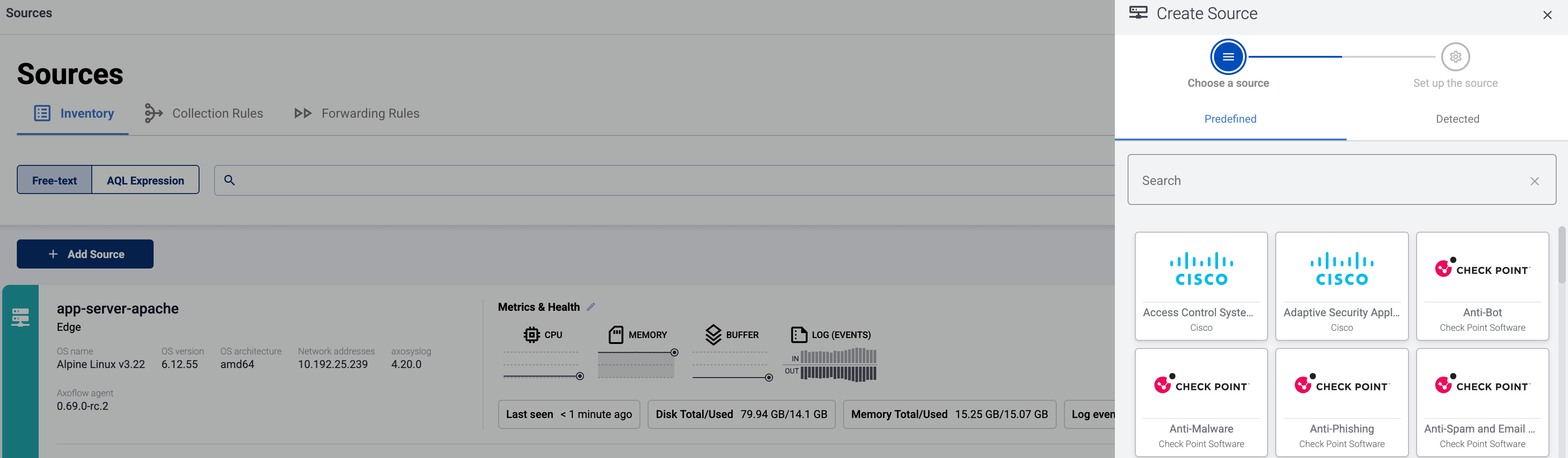
* If the source is actively sending data to an AxoRouter instance, select **Detected** , then select your source.
* Otherwise, select the vendor and product corresponding to your source from the **Predefined** sources, then enter the parameters of the source, like **IP address** and **FQDN**.
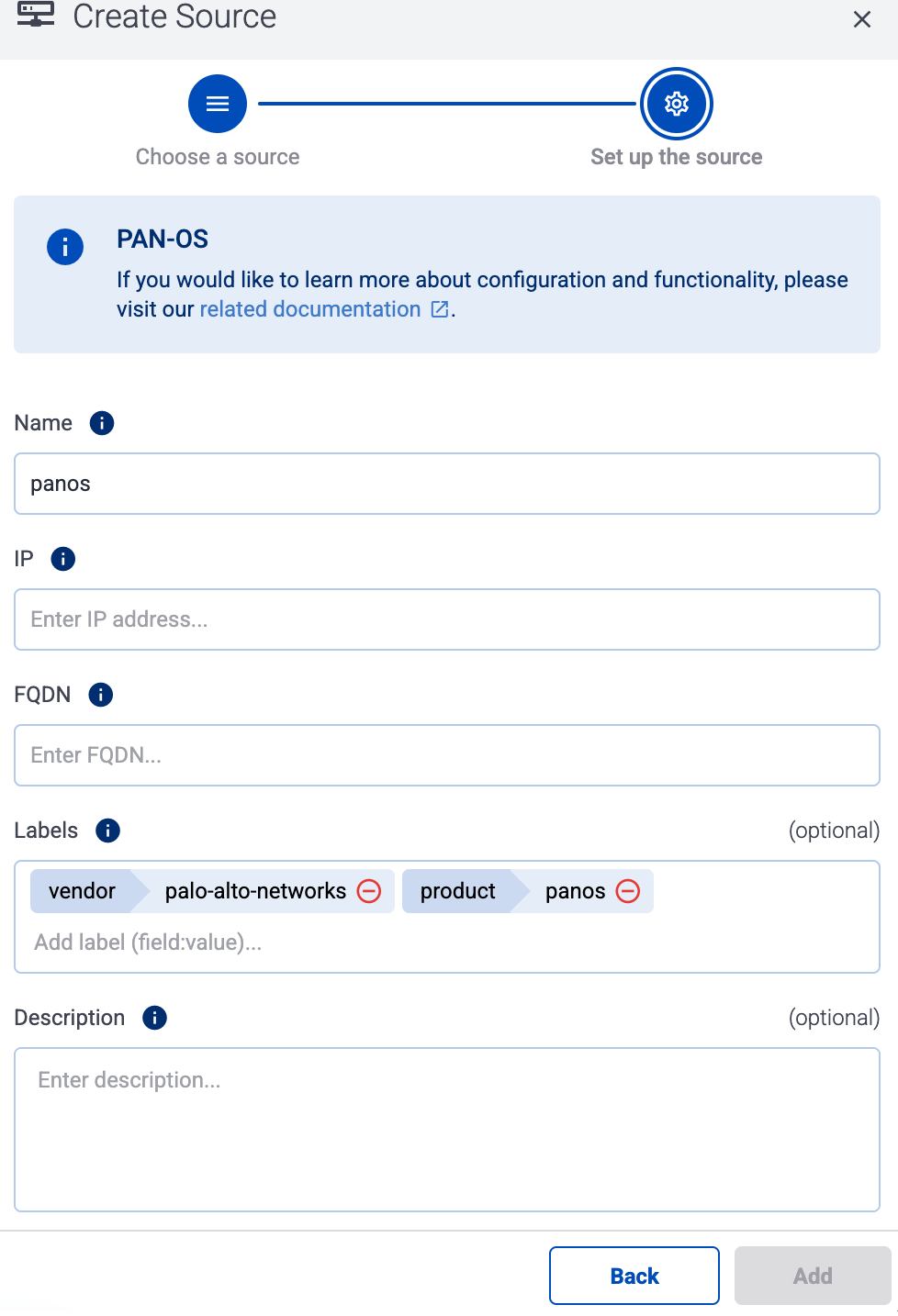
Note During [log tapping](../../../../docs/axoflow/onboard-hosts/log-tapping/index.md), you can add hosts that are actively sending data to an AxoRouter instance by clicking **Register source**.
3. (Optional) Add [custom labels](../../../../docs/axoflow/onboard-hosts/hosts/add-host-metadata/index.md) as needed.
4. Select **Add**.
5. (Optional) **Add Path** manually. That’s needed only when AxoConsole can’t detect the path based on the IP address and the FQDN, and you haven’t yet configured the source to send data to the router.
## Steps for SonicOS 6.x
Note: The steps involving the SonicWall user interface are just for your convenience, for details, see the [official SonicWall documentation]().
1. Log in to your SonicWall device. You need administrator privileges to perform the configuration.
2. Register the address of your AxoRouter as an Address Object.
1. Select **MANAGE > Policies > Objects > Address Objects**.
2. Click **Add**.
3. Configure the following settings:
* **Name** : Enter a name for the AxoRouter, for example, `AxoRouter`.
* **Zone Assignment** : Select the correct zone.
* **Type** : Select **Host**.
* **IP Address** : Enter the IP address of your AxoRouter: `%axorouter-ip%`
4. Click **Add**.
3. Set your AxoRouter as a syslog server.
1. Navigate to **MANAGE > Log Settings > SYSLOG**.
2. Click **ADD**.
3. Configure the following options:
* **Syslog ID** : Enter an ID for the firewall. This ID will be used as the hostname in the log messages.
* **Name or IP Address** : Select the Address Object of AxoRouter.
* **Server Type** : Select **Syslog Server**.
* Enable the **Enhanced Syslog Fields Settings**.
4. Click **OK**.
4. Add the source to AxoConsole.
1. Open the AxoConsole and select **Topology**.
2. Select **Add Item > Source**.
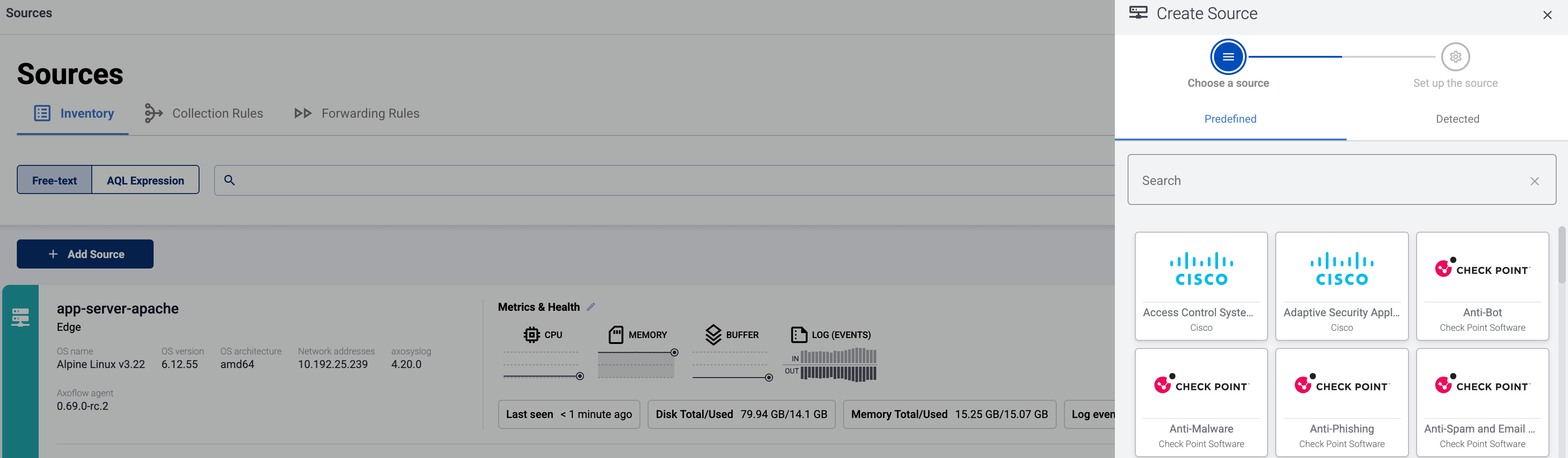
* If the source is actively sending data to an AxoRouter instance, select **Detected** , then select your source.
* Otherwise, select the vendor and product corresponding to your source from the **Predefined** sources, then enter the parameters of the source, like **IP address** and **FQDN**.
Note During [log tapping](../../../../docs/axoflow/onboard-hosts/log-tapping/index.md), you can add hosts that are actively sending data to an AxoRouter instance by clicking **Register source**.
3. (Optional) Add [custom labels](../../../../docs/axoflow/onboard-hosts/hosts/add-host-metadata/index.md) as needed.
4. Select **Add**.
5. (Optional) **Add Path** manually. That’s needed only when AxoConsole can’t detect the path based on the IP address and the FQDN, and you haven’t yet configured the source to send data to the router.
## Labels
Axoflow automatically adds the following labels to data collected from this source:
Analytics label | Message field | value
---|---|---
`vendor` | [`meta.vendor`](../../../../docs/axoflow/reference/message-schema/reference/index.md#meta.vendor) | `dell`
`product` | [`meta.product`](../../../../docs/axoflow/reference/message-schema/reference/index.md#meta.product) | `sonicwall`
You can use the labels as:
* **Filter labels** on the [Analytics page](../../../../docs/axoflow/metrics/analytics/index.md),
* in the **Filter By Label** field during [log tapping](../../../../docs/axoflow/onboard-hosts/log-tapping/index.md).
You can use the message fields
* in [Flow Processing steps](../../../../docs/axoflow/data-management/processing/index.md), for example, in the **Query** field of **Select Messages** steps,
* in AQL expressions in the search bars.
## Sending data to Splunk
When sending the data collected from this source to Splunk, Axoflow uses the following sourcetype and index settings:
sourcetype | index
---|---
`dell:sonicwall` | `netfw`
Tested with: [Dell SonicWall Add-on for Splunk technical add-on]()
If the Axoflow classification doesn’t set the source field for the message automatically, and you haven’t set it in a [flow processing step](../../../../docs/axoflow/data-management/processing/index.md#set-fields) manually (by setting the `meta.destination.splunk.source` field), AxoRouter automatically sets the source to the [name of the AxoRouter connector](../../../../docs/axoflow/reference/message-schema/reference/index.md#meta.connector.name) that received the message (for example, `axorouter-syslog-tcp-514`).
## Sending data to Google SecOps
When sending the data collected from this source to a [_dynamic_ Google SecOps destination](../../../../docs/axoflow/destinations/google/secops/index.md), Axoflow sets the following log type: `SONIC_FIREWALL`.
## Sending data to Microsoft Sentinel
When sending the data collected from this source to a [Microsoft Sentinel destination](../../../../docs/axoflow/destinations/microsoft/sentinel/index.md), Axoflow normalizes the data and sends it to the following table: `Syslog`.